
IoT Security Market Size, Share, Growth Opportunities & Latest Trends
IoT Security Market by Offering (Solutions and Services), Data Sensitivity (High-sensitivity Data, Low and Moderate-sensitivity Data), Application (Smart Manufacturing, Smart Government, Connected Healthcare, Smart Retail) - Global Forecast to 2031




OVERVIEW
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
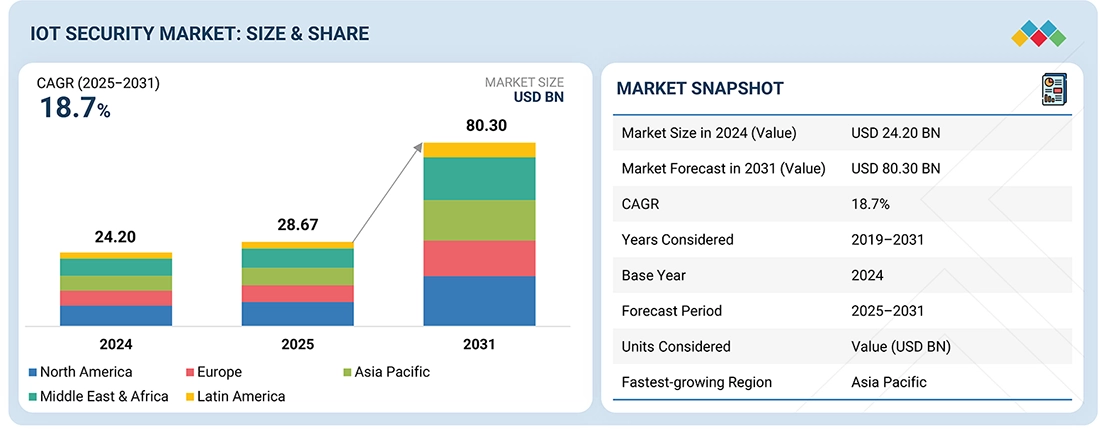
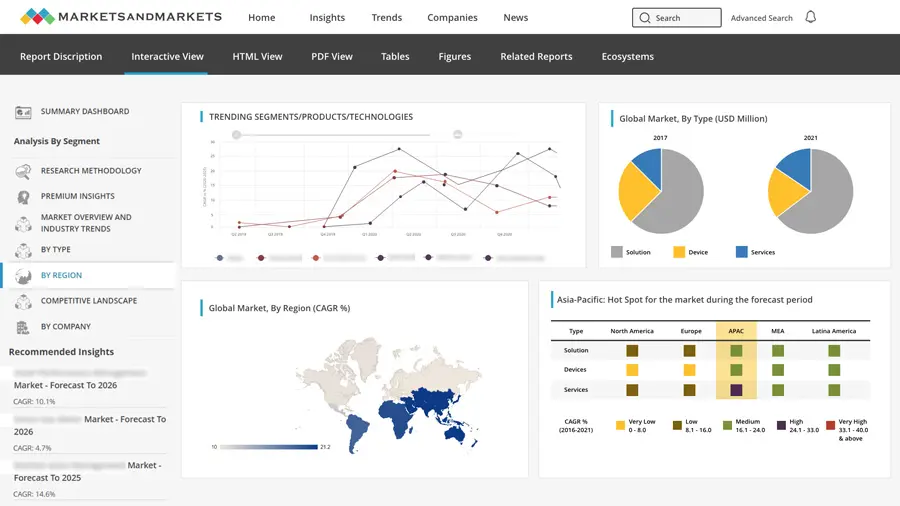
The IoT security market size is projected to grow from USD 28.67 billion in 2025 to USD 80.30 billion by 2031 at a Compound Annual Growth Rate (CAGR) of 18.7% during the forecast period. The IoT security market is showing impressive growth, with organizations continually implementing connected devices in industrial, enterprise, and consumer settings. IoT security involves technologies, practices, and processes that prevent cyber threats, unauthorized access, and data breaches to connected devices, networks, applications, and data. These security controls play a vital role in protecting interconnected infrastructure, integrity of the device, confidentiality of sensitive information data, and reliability of the IoT ecosystems in various industries including manufacturing, healthcare, energy, transportation, and smart cities.
KEY TAKEAWAYS
-
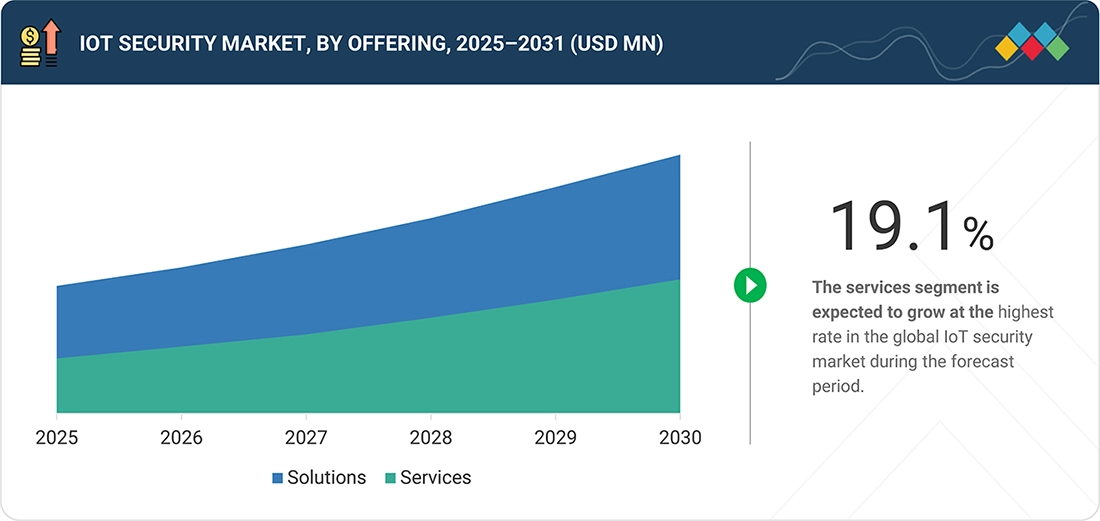
BY OFFERINGThe services segment is projected to lead in terms of growth rate.
-
BY APPLICATIONSmart manufacturing is estimated to dominate the market with a 24.1% market share in 2025.
-
COMPETITIVE LANDSCAPE - KEY PLAYERSMicrosoft, AWS, Cisco, Fortinet, Palo Alto Networks, IBM, Intel, Thales Group, NXP Semiconductors, and Infineon lead the IoT security market with strong capabilities in device authentication, network and endpoint security, encryption, IoT threat detection, IAM, and cloud-based IoT security platforms, supported by extensive enterprise ecosystems and global technology partnerships.
-
COMPETITIVE LANDSCAPE - STARTUPSAllot, Mobileum, and Entrust are agile players specializing in IoT network protection, device risk monitoring, identity security, and encryption technologies, enabling enterprises and telecom operators to strengthen security across connected devices and large-scale IoT environments.
In the IoT security market, the rapid expansion of connected devices across industrial, enterprise, and consumer environments is significantly increasing the cyber threat surface. The growing use of smart devices, industrial IoT systems, and connected infrastructure is driving demand for advanced security solutions such as device authentication, data encryption, network monitoring, and AI-driven threat detection. Rising concerns over data breaches, botnet attacks, and vulnerabilities in connected ecosystems are encouraging organizations to adopt comprehensive IoT security frameworks. Additionally, increasing regulatory requirements, the adoption of zero-trust architectures, and the need to secure critical infrastructure and smart environments are strengthening long-term demand for IoT security solutions and services.
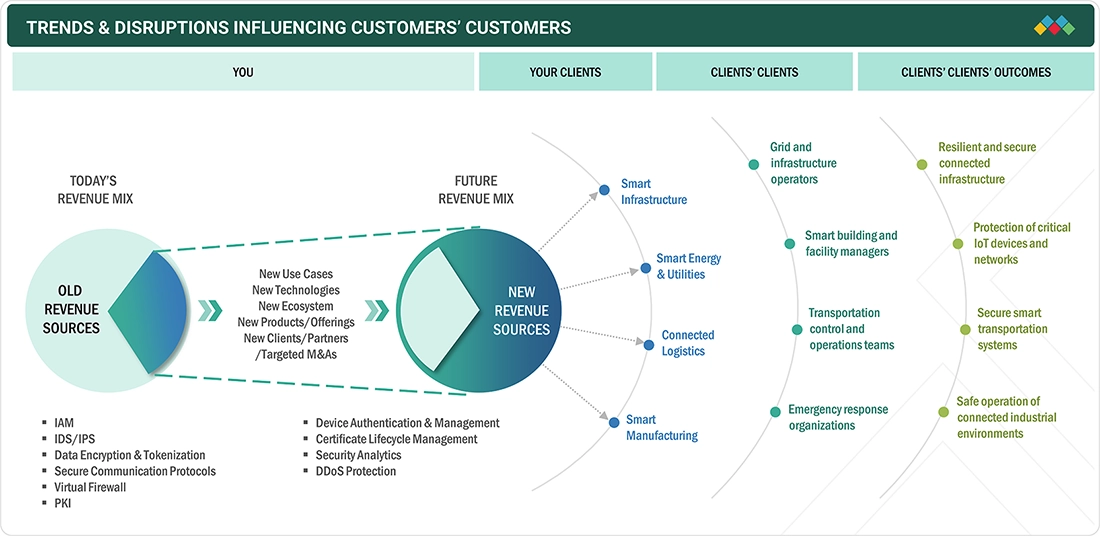
TRENDS & DISRUPTIONS IMPACTING CUSTOMERS' CUSTOMERS
The IoT security market is growing rapidly, driven by the surge in connected devices and the expansion of smart infrastructure across industries. Enterprises are shifting from basic network protection to advanced security solutions such as zero-trust architectures, AI-driven threat detection, device identity management, encryption, secure communication protocols, and cloud-based security platforms. Increasing investments in device authentication, security analytics, DDoS protection, and automated certificate management help organizations safeguard connected ecosystems, mitigate cyber threats, and ensure regulatory compliance across large-scale IoT deployments.
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
MARKET DYNAMICS
Level
-
Rapid proliferation of connected IoT devices across industries

-
Rising cyberattacks targeting IoT ecosystems and critical infrastructure
Level
-
High implementation and integration costs
-
Fragmented IoT standards and interoperability issues
Level
-
Growing adoption of AI-driven and zero-trust IoT security solutions
-
Expansion of space, satellite, and unmanned systems
Level
-
Limited visibility and monitoring of heterogeneous IoT devices
-
Shortage of skilled cybersecurity professionals
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
Driver: Rapid proliferation of connected IoT devices across industries
The rapid expansion of IoT deployments across sectors such as manufacturing, healthcare, smart cities, and transportation is significantly increasing the number of connected endpoints within enterprise networks. As organizations integrate sensors, gateways, and smart devices into operational environments, the potential attack surface expands considerably. This growth is driving the need for advanced IoT security solutions that can provide device authentication, network monitoring, threat detection, and secure communication across diverse and distributed IoT ecosystems.
Restraint: High implementation and integration costs
Implementing comprehensive IoT security solutions often requires significant investments in hardware security modules, encryption technologies, network monitoring tools, and security management platforms. Additionally, integrating these solutions into existing IT and operational technology (OT) environments can be complex and resource-intensive. For many organizations—particularly small and medium-sized enterprises—these high costs and integration challenges can slow adoption and limit large-scale deployment of IoT security technologies.
Opportunity: Growing adoption of AI-driven and zero-trust IoT security solutions
The increasing complexity of IoT ecosystems is encouraging the adoption of advanced security frameworks such as artificial intelligence-driven threat detection and zero-trust architectures. AI and machine learning enable real-time anomaly detection, automated threat response, and predictive security analytics across large volumes of IoT device data. As organizations seek more proactive and scalable approaches to securing connected environments, these intelligent security capabilities present significant growth opportunities for IoT security vendors.
Challenge: Limited visibility and monitoring of heterogeneous IoT devices
IoT environments typically consist of a wide range of devices with different operating systems, communication protocols, and security capabilities. Many of these devices lack built-in security features or standardized management interfaces, making it difficult for organizations to maintain full visibility and control over their IoT ecosystems. This fragmentation complicates continuous monitoring, vulnerability management, and threat detection, creating operational challenges for security teams attempting to protect large-scale and distributed IoT networks.
IOT SECURITY MARKET SIZE, SHARE, GROWTH OPPORTUNITIES & LATEST TRENDS: COMMERCIAL USE CASES ACROSS INDUSTRIES
| COMPANY | USE CASE DESCRIPTION | BENEFITS |
|---|---|---|
 |
A manufacturing enterprise deployed Cisco’s IoT security solutions to secure connected sensors and industrial devices across factory networks with device authentication and traffic monitoring. | Improved IoT asset visibility, reduced cyber risk from unauthorized devices, and stronger IT–IoT network segmentation. |
 |
A smart city authority implemented Palo Alto Networks’ IoT security platform to monitor and secure connected infrastructure, including traffic sensors, cameras, and smart lighting. | Real-time device identification, improved threat detection, reduced attack surface, and centralized IoT security management. |
 |
A healthcare provider used Microsoft Azure IoT security to protect connected medical devices, including patient monitors and imaging systems. | Enhanced device protection, improved regulatory compliance, early anomaly detection, and better visibility across hospital IoT networks. |
Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET ECOSYSTEM
The IoT security market is a collaborative ecosystem where device manufacturers, cloud providers, cybersecurity vendors, system integrators, and enterprises work together to secure connected devices and IoT infrastructure. Companies offer specialized solutions such as device authentication, network and endpoint protection, encryption, threat detection, identity and access management, and managed security services across industrial IoT, smart cities, healthcare, transportation, and consumer environments. Supported by evolving regulatory frameworks and security standards, organizations deploy these solutions to protect connected devices, sensitive data, and critical operations from increasingly sophisticated cyber threats targeting large-scale IoT ecosystems.
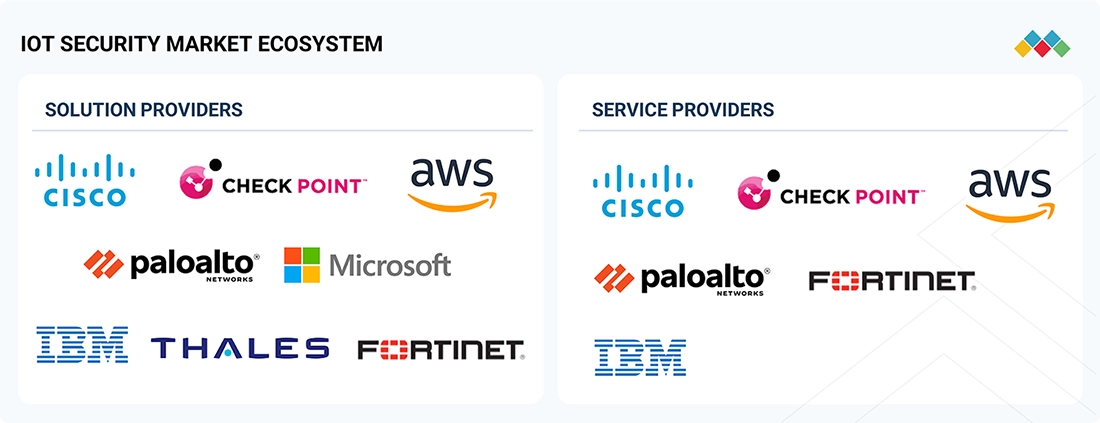
Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET SEGMENTS
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
IoT Security Market, by Offering
The solutions segment accounts for a significant share of the market, driven by the increasing deployment of connected devices across industrial, enterprise, and consumer environments. Organizations are prioritizing security solutions such as device authentication, network security, data encryption, identity and access management, and threat monitoring to protect large-scale IoT ecosystems. As connected devices continuously exchange sensitive operational and business data, enterprises require integrated security platforms that provide device visibility, real-time threat detection, and secure communication across edge, network, and cloud environments.
IoT Security Market, by Application
The smart manufacturing segment holds a leading share of the market due to the rapid adoption of Industrial IoT (IIoT), smart factories, connected sensors, robotics, and automated production systems. Manufacturing environments rely heavily on interconnected machines, industrial control systems, and real-time data exchange, which increases exposure to cyber threats. IoT security solutions help manufacturers secure production systems, prevent unauthorized device access, protect operational data, and ensure continuous and safe factory operations while supporting Industry 4.0 initiatives.
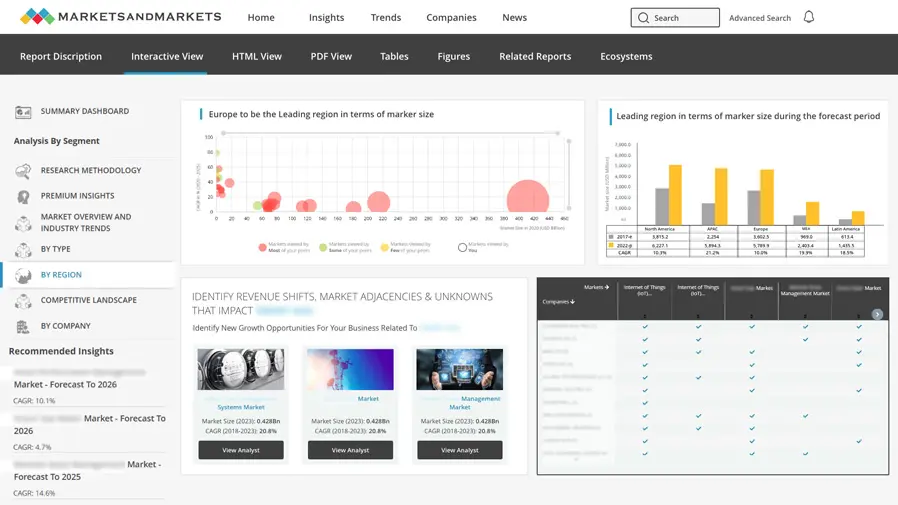
REGION
India to be fastest-growing region in global IoT security market during forecast period
The IoT security market in Asia Pacific is gaining strong momentum, with India projected to be the fastest-growing country due to rapid expansion of smart cities, industrial IoT, and connected infrastructure. Increasing deployment of connected devices across manufacturing, healthcare, transportation, and utilities is accelerating the adoption of AI-driven threat detection, zero-trust architectures, device authentication, and network security solutions, strengthening protection against evolving cyber threats targeting large-scale IoT ecosystems.
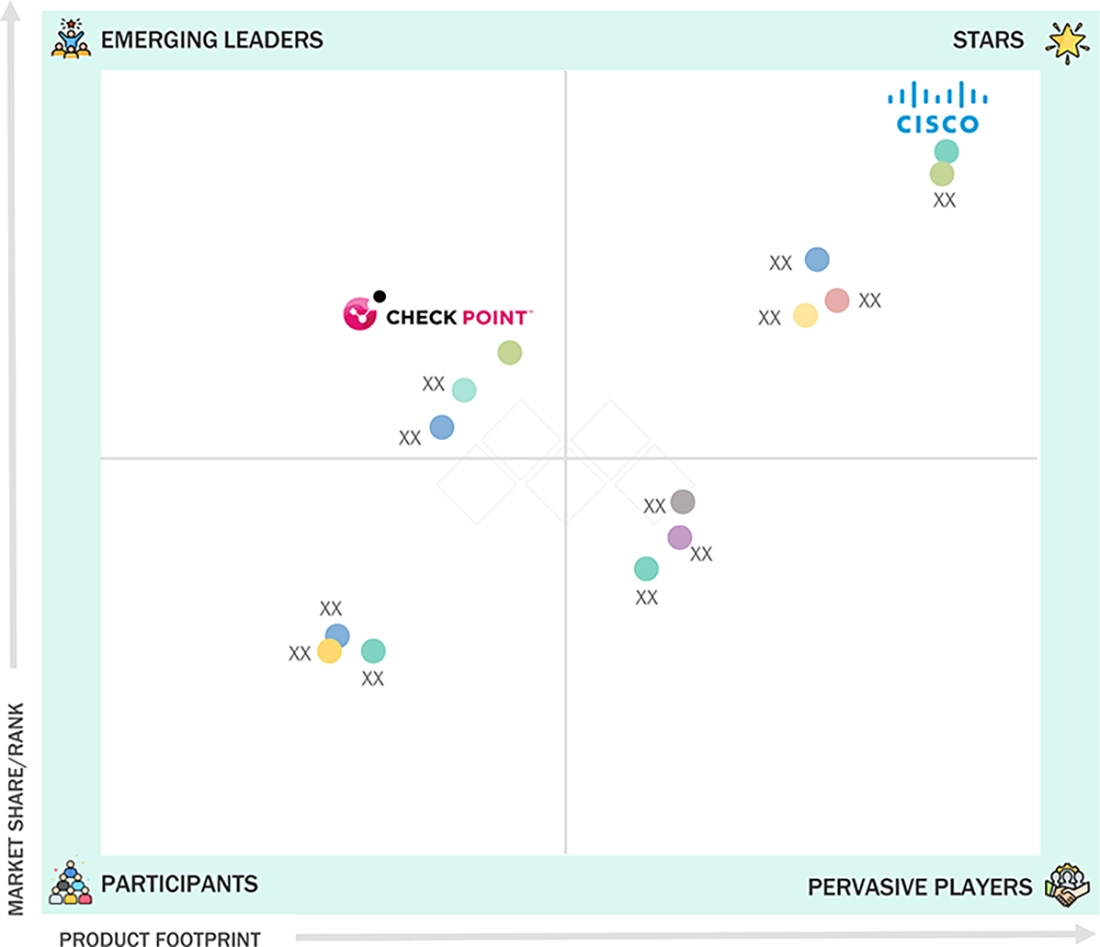
IOT SECURITY MARKET SIZE, SHARE, GROWTH OPPORTUNITIES & LATEST TRENDS: COMPANY EVALUATION MATRIX
The IoT security market features a mix of established global technology leaders and specialized cybersecurity innovators. Cisco, a “star” player, leads with advanced IoT security capabilities, including network segmentation, device visibility, threat detection, and secure access solutions, supporting large-scale enterprise and industrial IoT deployments. Check Point, an emerging player in IoT security, is expanding through IoT threat prevention, device risk assessment, automated security policy enforcement, and integrated network protection, strengthening security across enterprise and industrial IoT environments.
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
KEY MARKET PLAYERS
- Microsoft (US)
- Fortinet (US)
- AWS (US)
- IBM (US)
- Intel (US)
- Cisco (US)
- Thales Group (France)
- Infineon (Germany)
- Allot (Israel)
- Atos (France)
- Checkpoint (US)
- Palo Alto Networks (US)
- Mobileum (US)
- Entrust (US)
- NXP Semiconductors (Netherlands)
- Kaspersky (Switzerland)
MARKET SCOPE
| REPORT METRIC | DETAILS |
|---|---|
| Market Size, 2024 (Value) | USD 24.20 Billion |
| Market Forecast, 2031 (Value) | USD 80.30 Billion |
| Growth Rate | CAGR of 18.7% from 2025 to 2031 |
| Years Considered | 2019–2031 |
| Base Year | 2024 |
| Forecast Period | 2025–2031 |
| Units Considered | Value (USD Million/Billion) |
| Report Coverage | Revenue Forecast, Company Ranking, Competitive Landscape, Growth Factors, and Trends |
| Segments Covered |
|
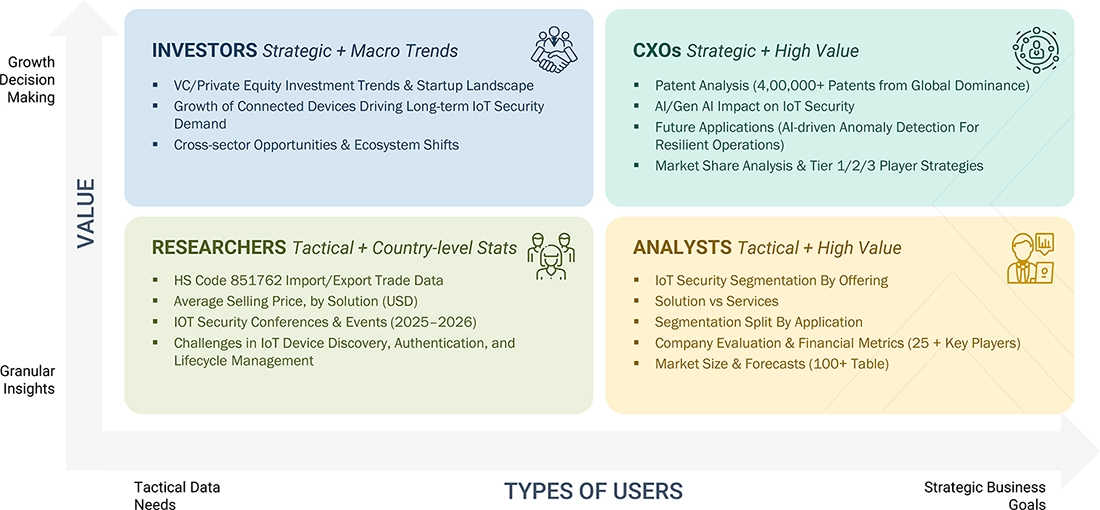
WHAT IS IN IT FOR YOU: IOT SECURITY MARKET SIZE, SHARE, GROWTH OPPORTUNITIES & LATEST TRENDS REPORT CONTENT GUIDE
DELIVERED CUSTOMIZATIONS
We have successfully delivered the following deep-dive customizations:
| CLIENT REQUEST | CUSTOMIZATION DELIVERED | VALUE ADDS |
|---|---|---|
| Leading IoT Platform & Device Provider | Benchmarking of key IoT security vendors across device authentication, network security, encryption, IoT threat detection, IAM, and cloud-based security platforms supporting large-scale IoT deployments. | Identifies competitive positioning, technology differentiation, and security capability alignment to strengthen IoT ecosystem security strategies. |
| IoT Security Service Provider | Profiling of major service providers offering managed IoT security services, device monitoring, vulnerability management, incident response, and IoT risk assessment across enterprise and industrial environments. | Highlights partnership opportunities, capability gaps, and go-to-market strategies for securing connected devices and IoT infrastructure. |
RECENT DEVELOPMENTS
- January 2026 : Microsoft introduced new IoT security capabilities within Microsoft Defender for IoT, enhancing device discovery, vulnerability management, and threat detection for connected industrial and enterprise environments. The update strengthens visibility across IT and OT networks, enabling organizations to detect anomalous IoT behavior, reduce attack surfaces, and secure large-scale connected device deployments.
- October 2025 : Fortinet expanded its Fortinet Security Fabric with enhanced IoT and OT security features integrated into FortiGate and FortiNAC platforms. The enhancements enable automated device identification, segmentation, and real-time threat monitoring across industrial networks, helping organizations secure IoT devices, reduce operational risks, and maintain regulatory compliance.
- November 2024 : Amazon Web Services (AWS) expanded its IoT security portfolio with new capabilities in AWS IoT Device Defender and AWS IoT FleetWise, enabling organizations to monitor device behavior, enforce security policies, and detect vulnerabilities across large fleets of connected devices. The update strengthens cloud-to-device security, improving protection for industrial, automotive, and smart infrastructure IoT deployments.
Table of Contents

Methodology
The study involved major activities in estimating the current market size for the IoT security market. Exhaustive secondary research was done to collect information on the IoT security industry. The next step was to validate these findings, assumptions, and sizing with industry experts across the value chain using primary research. Different approaches, such as top-down and bottom-up, were employed to estimate the total market size. After that, the market breakdown and data triangulation procedures were used to estimate the market size of the segments and subsegments of the IoT security market segments and subsegments of the IoT security market.
Secondary Research
The market for companies offering IoT security solutions is determined by secondary data available through paid and unpaid sources, analyzing the product portfolios of the major companies in the ecosystem, and rating the companies by their performance and quality. Various sources were referred to in the secondary research process to identify and collect information for this study. The secondary sources include annual reports, press releases, investor presentations of companies, white papers, journals, certified publications, and articles from recognized authors, directories, and databases.
In the secondary research process, various secondary sources were referred to for identifying and collecting information related to the study. Secondary sources included annual reports, press releases, investor presentations of IoT security vendors, forums, certified publications, and whitepapers. The secondary research was used to obtain critical information on the industry’s value chain, the total pool of key players, market classification, and segmentation from market and technology-oriented perspectives and segmentation from the market and technology-oriented perspectives.
Primary Research
In the primary research process, various primary sources from both the supply and demand sides were interviewed to obtain qualitative and quantitative information for this report. The primary sources from the supply side included industry experts, such as Chief Executive Officers (CEOs), Vice Presidents (VPs), marketing directors, technology and innovation directors, and related key executives from various key companies and organizations operating in the IoT security market.
After the complete market engineering (calculations for market statistics, market breakdown, market size estimations, market forecasting, and data triangulation), extensive primary research was conducted to gather information and verify and validate the critical numbers arrived at. Primary research was also conducted to identify the segmentation types, industry trends, competitive landscape of IoT security solutions offered by various market players, and key market dynamics, such as drivers, restraints, opportunities, challenges, industry trends, and key player strategies.
In the complete market engineering process, the top-down and bottom-up approaches were extensively used, along with several data triangulation methods, to perform the market estimation and market forecasting for the overall market segments and subsegments listed in this report. Extensive qualitative and quantitative analysis was performed on the complete market engineering process to list the key information and insights throughout the report to list the key information/insights throughout the report.
BREAKDOWN OF PRIMARY INTERVIEW PARTICIPANTS
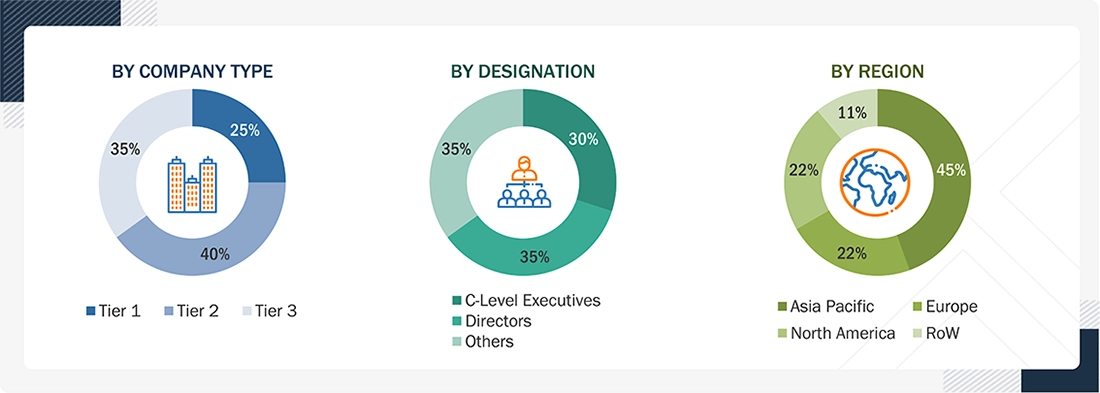
Others include sales managers, marketing managers, and product managers.
Note: Tier 1 companies are those with total annual revenue > USD 10 billion; tier 2 companies are those with total annual revenue between USD 1 and 10 billion; and tier 3 companies are those with total annual revenue between USD 500 million and 1 billion
RoW includes the Middle East & Africa, and Latin America
To know about the assumptions considered for the study, download the pdf brochure
Market Size Estimation
Top-down and bottom-up approaches were used to estimate and validate the size of the global IoT security market and estimate the size of various other dependent sub-segments in the overall IoT security market.
The research methodology used to estimate the market size includes the following details:
- Key players in the market were identified through secondary research, and their market shares in the respective regions were determined through primary and secondary research. This entire procedure included the study of the annual and financial reports of the top market players, and extensive interviews were conducted for key insights from the industry leaders, such as CEOs, VPs, directors, and marketing executives.
- All percentage splits and breakdowns were determined using secondary sources and verified through primary sources. All possible parameters that affect the market covered in this research study have been accounted for, viewed in extensive detail, verified through primary research, and analyzed to get the final quantitative and qualitative data. This data is consolidated and added to detailed inputs and analysis from MarketsandMarkets.
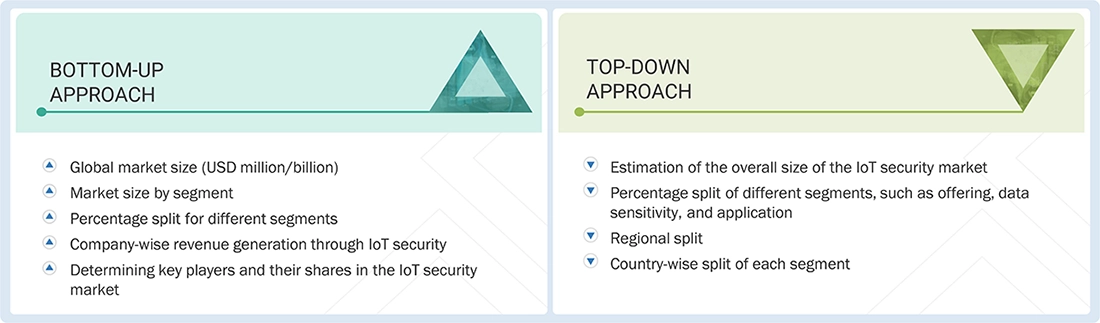
Data Triangulation
After arriving at the overall market size using the market size estimation processes explained above, the market was split into several segments and subsegments. The data triangulation and market breakup procedures were employed, wherever applicable, to complete the overall market engineering process and arrive at the exact statistics of each market segment and subsegment. The data was triangulated by studying various factors and trends from both the demand and supply sides.
Market Definition
IoT security is the practice of securing IoT devices and the networks they are connected to. The interconnectedness of IoT presents a substantial challenge to enterprises in terms of security risks arising from shadow devices connected to the network. IoT security solutions and services minimize IoT security concerns and protect organizations, people, processes, and data from threats, thus lowering the losses caused by cyberattacks on connected devices.
Key Stakeholders
- Global managed service providers
- Cloud Service Providers (CSPs)
- Independent Software Vendors (ISVs)
- System integrators
- Value-added Resellers (VARs)
- Chief Financial Officers (CFOs)
- Information Technology (IT) Directors
- Small and Medium-sized Enterprises (SMEs)
- IT strategy consultants
- Technology partners
- Research organizations
- Enterprise users
Report Objectives
- To define, describe, and forecast the IoT security market based on offering, solution, application, and region.
- To provide detailed information about the major factors (drivers, opportunities, restraints, and challenges) influencing the growth of the market
- To analyze opportunities for stakeholders by identifying the high-growth segments of the market
- To forecast the size of the market segments with respect to five main regions: North America, Europe, Asia Pacific, the Middle East & Africa, and Latin America
- To analyze subsegments of the market with respect to individual growth trends, prospects, and contributions to the overall market
- To profile the key players and comprehensively analyze their market sizes and core competencies
- To track and analyze competitive developments such as product enhancements and product launches, acquisitions, and partnerships & collaborations in the market globally.
Available customizations:
With the given market data, MarketsandMarkets offers customizations based on company-specific needs. The following customization options are available for the report:
Company information
- Detailed analysis and profiling of additional market players (up to 5)
Need a Tailored Report?
Customize this report to your needs
Get 10% FREE Customization
Customize This ReportPersonalize This Research
- Triangulate with your Own Data
- Get Data as per your Format and Definition
- Gain a Deeper Dive on a Specific Application, Geography, Customer or Competitor
- Any level of Personalization
Let Us Help You
- What are the Known and Unknown Adjacencies Impacting the IoT Security Market
- What will your New Revenue Sources be?
- Who will be your Top Customer; what will make them switch?
- Defend your Market Share or Win Competitors
- Get a Scorecard for Target Partners
Custom Market Research Services
We Will Customise The Research For You, In Case The Report Listed Above Does Not Meet With Your Requirements
Get 10% Free Customisation













Growth opportunities and latent adjacency in IoT Security Market