
Artificial Intelligence in Cybersecurity Market
AI in Cybersecurity Market by Solution (AI-native Security, AI-enhanced Security Products), Security Type (Endpoint Security & Management, Network Security, Application Security, Cloud Security, Data Security, IAM, Encryption & Tokenization, Cybersecurity Operation Solutions) - Global Forecast to 2031




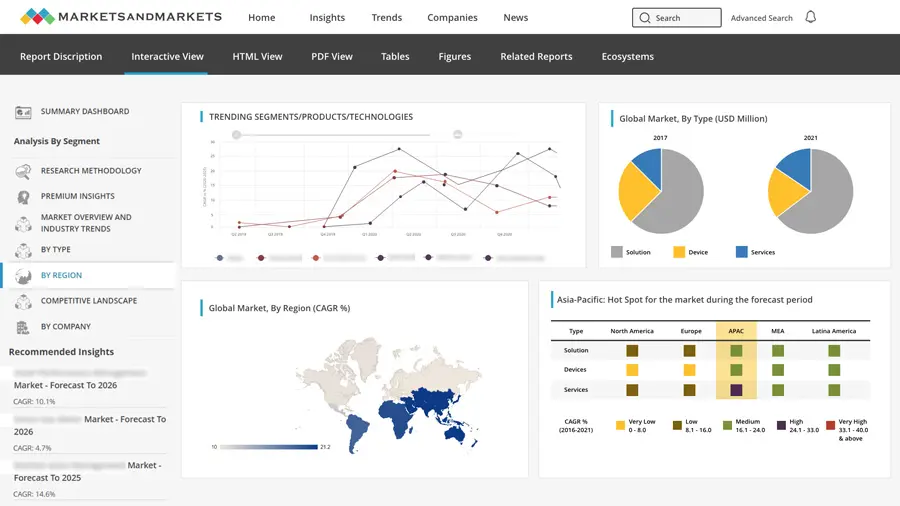
OVERVIEW
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
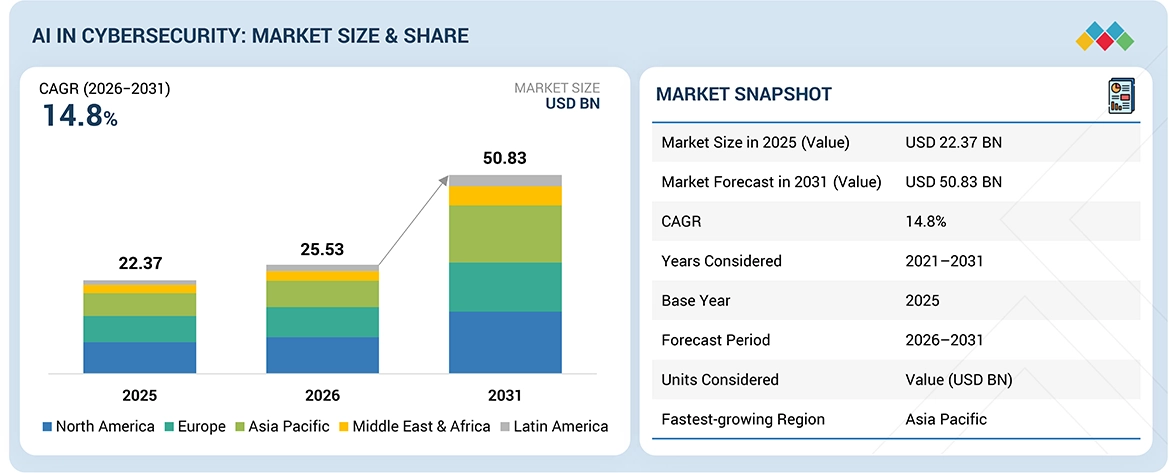
The AI in cybersecurity market was a valuation of USD 25.53 billion in 2026. By 2031, it's expected to reach USD 50.83 billion, reflecting a compound annual growth rate (CAGR) of 14.8%. The increasing market growth has been driven by high enterprise adoption of AI in sectors such as financial, retail, healthcare, and technology, where AI-enabled cybersecurity has been used to monitor attacks and analyze large security data to help make faster decisions for various cybersecurity operations. Organizations are deploying artificial intelligence across security operations to automatically incorporate detections of anomalous activity, accelerate responses to incidents, and bolster security at cloud, network, and endpoint. The rising adoption of threat intelligence, security analytics platforms, and identity protection through AI adoption is a growing enterprise use case in the cybersecurity landscape.
KEY TAKEAWAYS
-
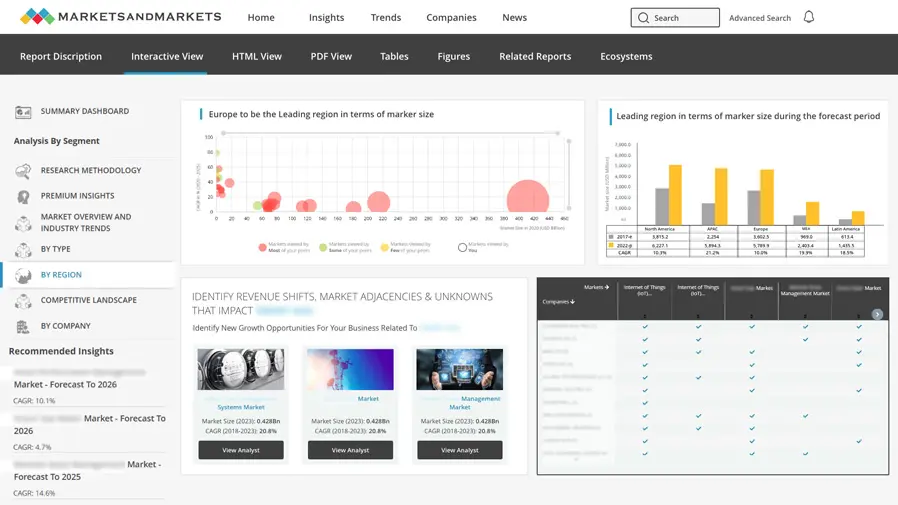
By RegionNorth America is estimated to account for the largest market share of 35.50% in 2026.
-
By OfferingThe software segment is projected to hold the largest market share in 2026.
-
By Security TypeThe endpoint security & management segment is positioned to hold the largest market share of 18.75% in 2026.
-
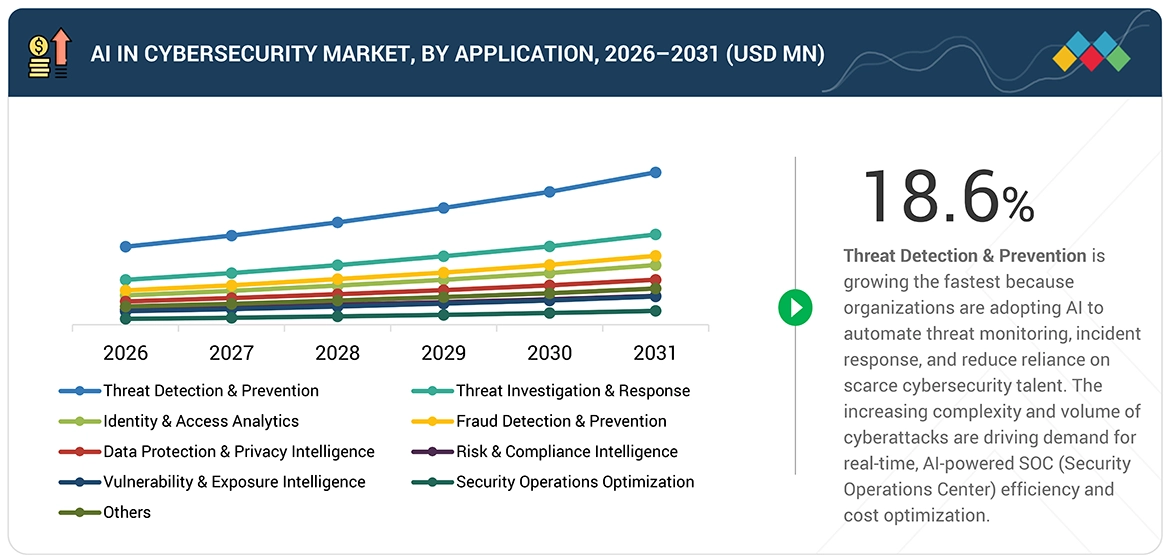
By ApplicationThe security operations optimization segment is projected to showcase the highest CAGR of 18.6% during the forecast period.
-
By VerticalThe retail & e-commerce segment is projected to grow at the highest CAGR during the forecast period.
-
Competitive Landscape - Key PlayersMicrosoft, Palo Alto Networks, and AWS are among the leading players in the AI in cybersecurity market, given their strong market share and product portfolios.
-
Competitive Landscape - Startups/SMEsDeep Instinct, Nozomi Networks, and Acalvio Technologies have distinguished themselves among other players by securing strong footholds in specialized niche areas, underscoring their potential as emerging leaders.
Many global initiatives are accelerating the adoption of AI in cybersecurity as organizations focus on improving threat detection and response across ever more complex environments. Adoption is being further driven by the increasing need for automated SOC workflows and faster incident response via platforms including SOAR and XDR, as well as rising adoption of AI for securing cloud workloads and APIs. Technology vendors, meanwhile, are expanding infrastructure to enable these use cases, including AI-enabled security platforms and high-performance computing infrastructures.
TRENDS & DISRUPTIONS IMPACTING CUSTOMERS' CUSTOMERS
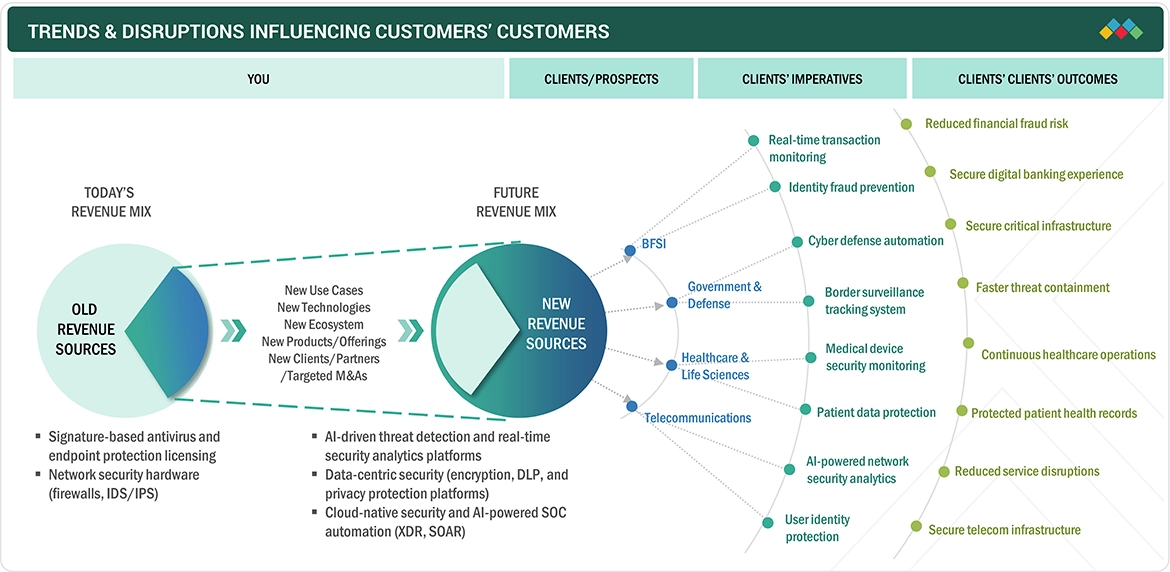
The cybersecurity landscape is evolving. There is a shift away from the old, reactive security measures and toward smart, data-powered platforms that can respond automatically and in real time. Companies are now weaving AI into various security tools, such as identity management, data protection, and network security, all in an effort to make better decisions. This change is causing a significant shake-up, allowing vendors to build unified, scalable security systems that adapt to the changing needs of both businesses and their partners.
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
MARKET DYNAMICS
Level
-
Increasing complexity and frequency of cyberattacks driving AI adoption

-
AI-powered cloud workload & API security
Level
-
Limited availability of quality data and privacy concerns restricting AI effectiveness
-
Growth of AI-driven cloud security posture management (CSPM) & workload protection platforms
Level
-
Rising need for automated security operations creating growth opportunities
-
The growing use of artificial intelligence in identity threat detection and response (ITDR)
Level
-
Evolving adversarial threats posing challenges to AI-based cybersecurity systems
-
The use of shadow AI is creating unmonitored vulnerabilities in enterprise applications
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
Driver – Increasing complexity and frequency of cyberattacks driving AI adoption
The rising frequency and complexity of cyberattacks, including zero-day exploits and AI-powered threats, are driving the adoption of AI in cybersecurity. Organizations are leveraging AI for real-time threat detection, anomaly identification, and faster response. The growing attack surface across cloud, endpoints, and networks further accelerates demand for advanced AI-driven cybersecurity solutions and services.
Restraint – Limited availability of quality data and privacy concerns restricting AI effectiveness
The efficacy of AI models also relies on the availability of large amounts of quality security information, which may not be feasible owing to privacy concerns and organizational barriers. Furthermore, the fear of sharing information may also be a challenge in the development of AI-based cybersecurity tools.
Opportunity – Rising need for automated security operations creating growth opportunities
The increasing need to manage alert volumes and reduce response times is creating strong demand for AI-driven security operations platforms. Technologies such as XDR, SOAR, and AI copilots are enabling automation of threat detection and response. This shift toward autonomous and intelligent security operations presents significant growth opportunities for vendors offering AI-powered security platforms, automation solutions, and managed security services.
Challenge – Evolving adversarial threats posing challenges to AI-based cybersecurity systems
Cybercriminals are increasingly using AI to develop more sophisticated attacks, which are difficult to evade. They are also using adversarial attacks, which are difficult to detect by AI models. Therefore, it is a continuous process for both attackers and defenders. Robustness, explainability, and robustness are challenges in this context.
ARTIFICIAL INTELLIGENCE IN CYBERSECURITY MARKET: COMMERCIAL USE CASES ACROSS INDUSTRIES
| COMPANY | USE CASE DESCRIPTION | BENEFITS |
|---|---|---|
 |
A financial investment organization implemented zero-trust security, including SASE, endpoint security, and network security at Infosys. | The deployment improved threat detection, enabled centralized management, sped up incident response, and strengthened security policy compliance. |
 |
Used AWS-based cybersecurity platform (SageMaker, Glue, Lambda, S3) to detect and analyze large-scale cyber threats in real-time. | Exceeded cybersecurity benchmarks, processes 60,000 threats/sec, enables fast forensic analysis without performance impact, and operates efficiently with a small team. |
 |
Using model from Snorkel Flow, US national security teams can develop AI/ML applications that utilize text, voice, and satellite data to accelerate intelligence work. | Platform minimizes manual labeling effort, increases scalability, gives more transparent models and higher performance with easier troubleshooting. |
Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET ECOSYSTEM
The AI in cybersecurity ecosystem comprises software and service providers that develop advanced threat detection systems, analytics tools, and comprehensive security platforms. Together, these components work seamlessly to safeguard digital environments. This integrated approach delivers a holistic suite of cybersecurity solutions, effectively protecting both enterprise and cloud infrastructures.

Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET SEGMENTS
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
AI in Cybersecurity Market, By Offering
Software will take the biggest share by 2026 because more businesses are using AI-based security tools. Companies want solutions that can quickly detect threats and handle them automatically. The growing use of cloud platforms is also pushing the demand for software even higher.
AI in Cybersecurity Market, By Security Type
Cloud security is expected to grow the fastest. This is because more companies are moving to the cloud and using multiple cloud services. AI helps them spot threats, fix issues, and manage security problems in real time. The shift toward cloud-native systems and zero-trust security is also increasing the need for these solutions.
AI in Cybersecurity Market, By Application
Threat detection and prevention is expected to grow the fastest as companies focus more on finding and stopping cyber threats early. Tools powered by AI, like anomaly detection and behavior analysis, are becoming important for real-time protection. As cyberattacks become more complex, the need for these tools is increasing.
AI in Cybersecurity Market, By Vertical
The BFSI sector has the largest market share, given that this sector is more prone to cyber attacks and has strict regulations. There is a rise in the adoption of AI in banks and financial institutions for fraud prevention. There is also a rise in digital transactions.
REGION
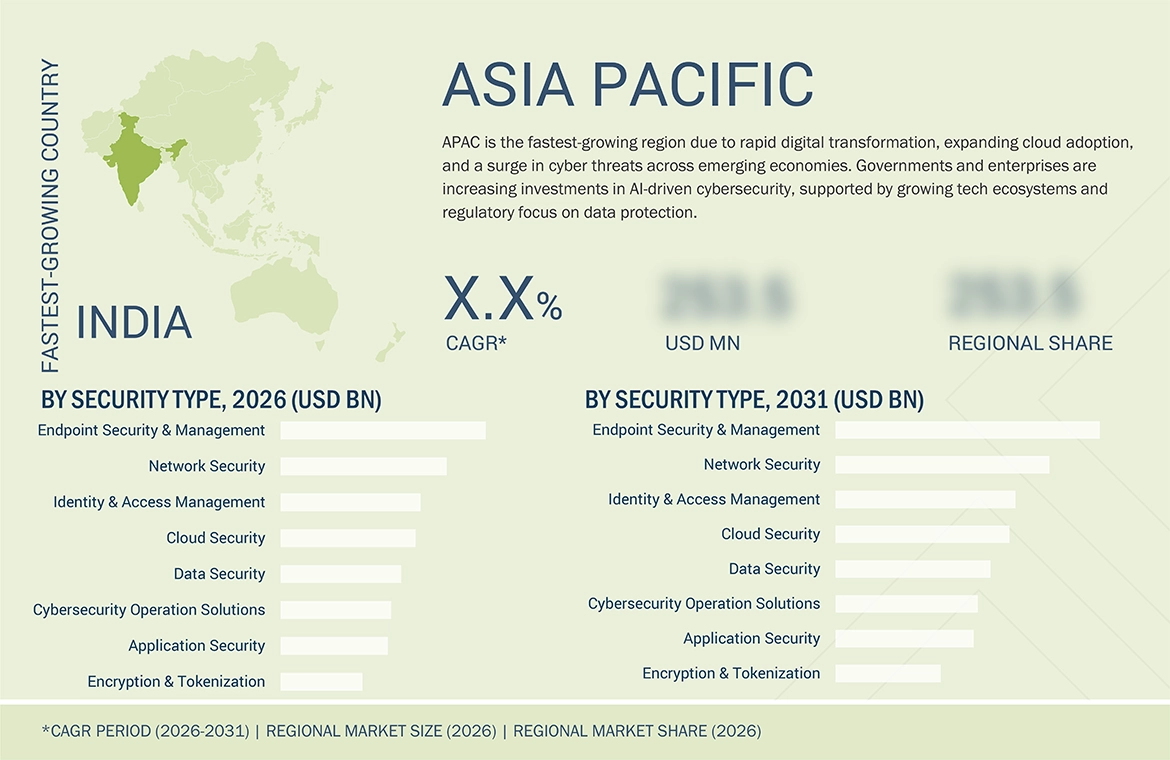
Asia Pacific is expected to be the fastest-growing region in the AI in cybersecurity market during the forecast period.
Asia Pacific is poised to outpace all others in the AI in cybersecurity market, according to projections. This surge is fueled by the region's swift digital transformation and the widespread embrace of AI by businesses. The growth is further bolstered by the escalating number and complexity of cyber threats. Asia Pacific is a major victim of cyber incidents worldwide, and the frequency of attacks shows no sign of abating. Organizations are investing in AI-driven security solutions to improve threat detection, protect critical infrastructure, and strengthen resilience across digital environments.
ARTIFICIAL INTELLIGENCE IN CYBERSECURITY MARKET: COMPANY EVALUATION MATRIX
The Company Evaluation Matrix places Palo Alto Networks in the stars quadrant, driven by its strong AI-driven cybersecurity portfolio, integrated platform approach, and broad enterprise adoption. IBM is positioned in the emerging leaders quadrant as it continues to expand its AI-enabled security offerings, particularly in security operations and threat intelligence, supported by its focus on hybrid cloud and enterprise security solutions.
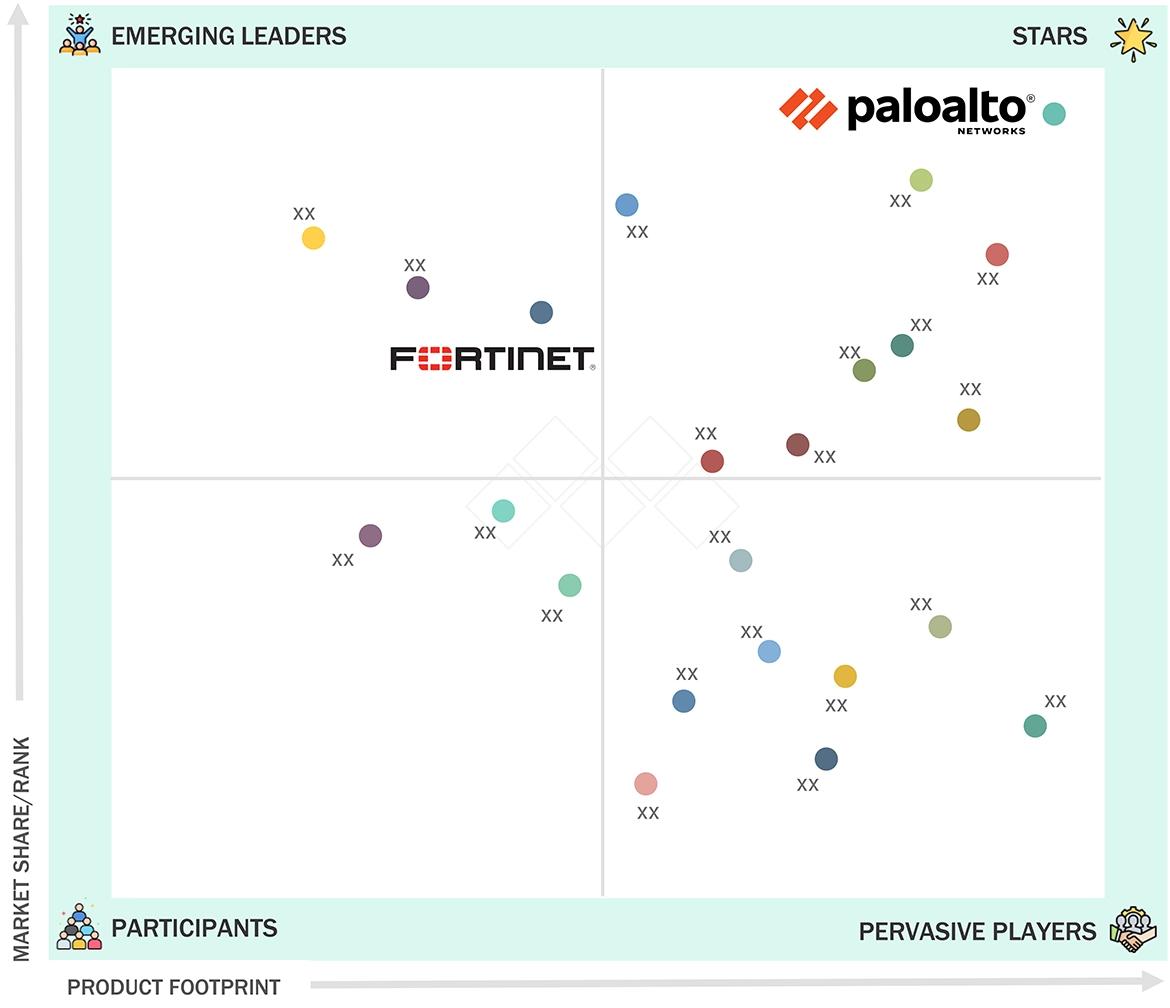
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
KEY MARKET PLAYERS
- NVIDIA (US)
- Intel (US)
- AMD (US)
- Samsung Electronics (South Korea)
- Micron Technology (US)
- IBM (US)
- AWS (US)
- Microsoft Corporation (US)
- Palo Alto Networks Inc. (US)
- Trellix (US)
- CrowdStrike (US)
- Gen Digital (US)
- BlackBerry (Canada)
- LexisNexis (US)
- Securonix Inc. (US)
- Sift Science (US)
MARKET SCOPE
| REPORT METRIC | DETAILS |
|---|---|
| Market Size in 2025 (Value) | USD 22.37 Billion |
| Market Size in 2026 (Value) | USD 25.53 Billion |
| Market Forecast in 2031 (Value) | USD 50.83 Billion |
| CAGR | 14.8% |
| Years Considered | 2021-2031 |
| Base Year | 2025 |
| Forecast Period | 2026-2031 |
| Units Considered | USD Billion/Million |
| Report Coverage | Revenue forecast, company ranking, competitive landscape, growth factors, and trends |
| Segments Covered |
|
| Regions Covered | North America, Asia Pacific, Europe, Middle East & Africa, Latin America |
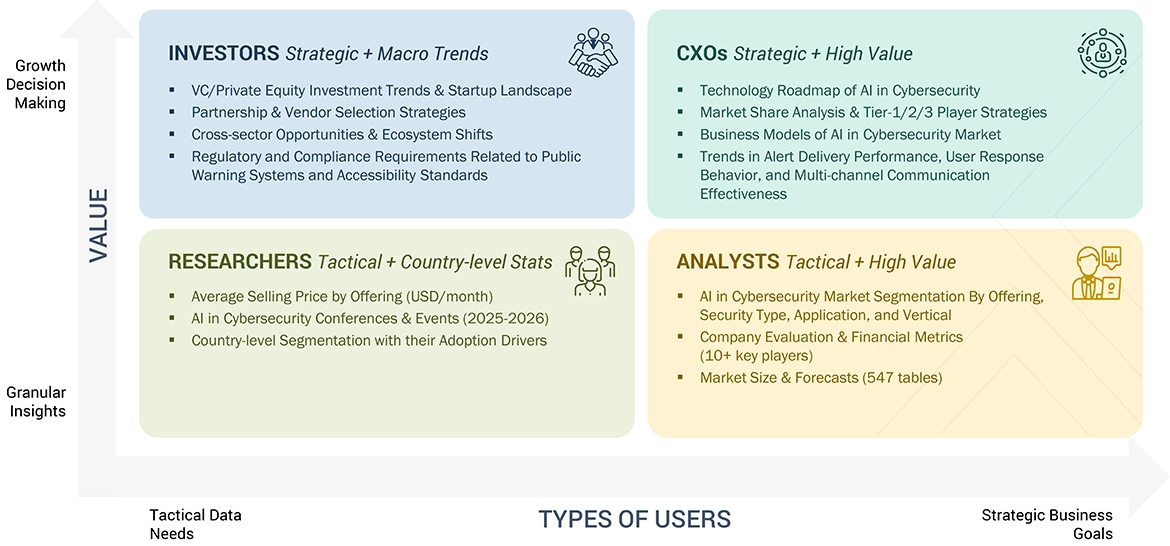
WHAT IS IN IT FOR YOU: ARTIFICIAL INTELLIGENCE IN CYBERSECURITY MARKET REPORT CONTENT GUIDE
DELIVERED CUSTOMIZATIONS
We have successfully delivered the following deep-dive customizations:
| CLIENT REQUEST | CUSTOMIZATION DELIVERED | VALUE ADDS |
|---|---|---|
| Leading BFSI Firm |
|
|
| Leading Telecommunication Vendor |
|
|
RECENT DEVELOPMENTS
- March 2026 : Palo Alto Networks launched a secure browser designed for modern digital environments, increasing protection against emerging risks from advanced workflows. The move strengthens its platform strategy and focus on securing the evolving enterprise workspace.
- March 2026 : Microsoft introduced enhanced security features in 2026 through its Security Copilot, significantly increasing the ability of teams to detect threats in real-time and respond faster. The system increases efficiency by analyzing large volumes of security data and delivering actionable insights.
- February 2026 : Google Cloud introduced advanced security features for threat management, increasing the speed of threat detection, strengthening identity protection, and enhancing automated response capabilities.
Table of Contents

Methodology
The research methodology for the AI in cybersecurity market report relied on extensive secondary sources and directories, as well as reputable open-source databases, to identify and collect relevant information for this technical and market-oriented study. In-depth interviews were conducted with primary respondents, including end users, senior executives from multiple companies offering AI in cybersecurity solutions and services, and industry consultants, to obtain and verify critical qualitative and quantitative information and to assess market prospects and industry trends.
Secondary Research
During the secondary research process, various secondary sources were consulted to identify and collect information for the study. The secondary sources included annual reports, press releases, and investor presentations of companies; white papers; and certified publications.
Secondary research was used to gather key information on the industry’s value chain, the market’s monetary chain, the overall pool of key players, market classification, and segmentation based on industry trends, regional markets, and key developments from both market and technology-oriented perspectives.
Primary Research
In the primary research process, a diverse range of stakeholders from both the supply and demand sides of the AI in cybersecurity ecosystem were interviewed to gather qualitative and quantitative insights specific to this market. From the supply side, key industry experts, such as chief executive officers (CEOs), vice presidents (VPs), marketing directors, technology & innovation directors, and technical leads from vendors offering AI in cybersecurity software & services, were consulted. Additionally, system integrators, service providers, and IT service firms that implement and support the AI in cybersecurity solutions were included in the study. On the demand side, input from IT decision-makers, infrastructure managers, and business heads from prominent industry verticals was collected to understand user perspectives and adoption challenges within the targeted industries.
The primary research ensured that all crucial parameters affecting the AI in cybersecurity market, including technological advancements and evolving use cases, as well as regulatory and compliance needs, were considered. Each factor was thoroughly analyzed, verified through primary research, and evaluated to obtain precise quantitative and qualitative data for this market.
Once the initial phase of market engineering was completed, which included detailed calculations for market statistics, segment-specific growth forecasts, and data triangulation, a second round of primary research was conducted. This step was crucial for refining and validating critical data points, such as AI in cybersecurity offerings (software, and services), industry adoption trends, the competitive landscape, and key market dynamics like demand drivers (Automated SOC workflows & incident response (SOAR/XDR, AI-powered cloud workload & API security), challenges (Model inversion and data extraction attacks can expose sensitive training data and important business information), and opportunities (Growth of AI-driven cloud security posture management (CSPM) & workload protection platforms, growing use of artificial intelligence in identity threat detection and response (ITDR), restraints (Data silos are restricting unified thread visibility across endpoints, cloud, and network layers).
In the comprehensive market engineering process, the top-down and bottom-up approaches, along with several data triangulation methods, were extensively employed to estimate and forecast the overall market segments and subsegments listed in this report. Extensive qualitative and quantitative analysis was conducted across the complete market engineering process to capture critical information/insights throughout the report.
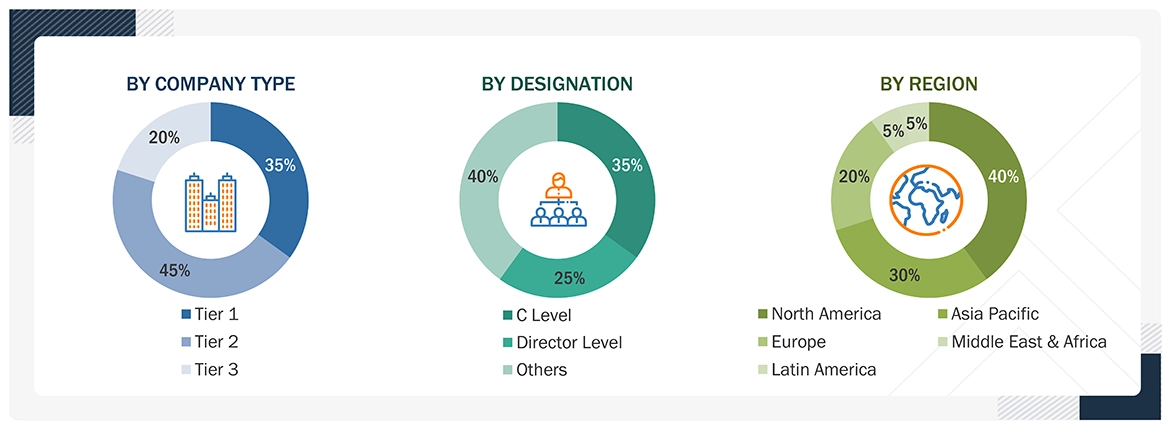
Note: Tier 1 companies' revenue is more than USD 10 billion; tier 2 companies' revenue ranges between USD 1 billion and USD 10 billion; and tier 3 companies' revenue ranges between USD 500 million and USD 1 billion.
To know about the assumptions considered for the study, download the pdf brochure
Market Size Estimation
The top-down and bottom-up approaches were employed to estimate and forecast AI in cybersecurity market, as well as its dependent submarkets. This multi-layered analysis was further reinforced through data triangulation, which incorporated primary and secondary research inputs. The market figures were also validated against the existing MarketsandMarkets repository for accuracy.
Artificial Intelligence in Cybersecurity Market : Top-Down and Bottom-Up Approach

Data Triangulation
The market was divided into several segments and subsegments after determining the overall market size using the market size estimation processes described above. To complete the overall market engineering process and determine the exact statistics for each market segment and subsegment, data triangulation and market segmentation procedures were employed, wherever applicable. The overall market size was then used in the top-down approach to estimate the size of other individual markets by applying percentage splits to the market segmentation.
Market Definition
According to NVIDIA, AI in cybersecurity represents an advanced approach that leverages accelerated computing and deep learning to detect, analyze, and respond to cyber threats in real time. It enables organizations to process vast volumes of security data across networks, endpoints, and cloud environments to identify anomalies and potential attacks with greater accuracy. By utilizing GPU-powered AI models and high-performance analytics, these solutions enhance threat intelligence, automate security operations, and improve response efficiency. AI-driven cybersecurity platforms support scalable, adaptive protection by continuously learning from evolving threat patterns and minimizing manual intervention. This approach plays a critical role in strengthening enterprise security posture, protecting digital assets, and ensuring resilient operations across modern IT infrastructures.
Key Stakeholders
- Vendors offering AI-powered cybersecurity
- Vendors offering cybersecurity for securing AI
- Business analysts
- Cloud hyperscalers
- Consulting service providers
- Enterprise end users
- Distributors and value-added resellers
- Government agencies
- Independent software vendors
- Managed service providers
- Market research and consulting firms
- Support & maintenance service providers
- System integrators (SIs)/Migration service providers
- Generative AI technology providers
Report Objectives
- To define, describe, and predict the AI in the cybersecurity market by offering (software and services), security type, application, and vertical
- To provide detailed information related to major factors (drivers, restraints, opportunities, and industry-specific challenges) influencing market growth
- To analyze opportunities in the market and provide details of the competitive landscape for stakeholders and market leaders
- To forecast the market size of segments with respect to five main regions: North America, Europe, Asia Pacific, the Middle East & Africa, and Latin America
- To analyze each submarket with respect to individual growth trends, prospects, and contributions to the overall AI in cybersecurity market
- To analyze competitive developments, such as partnerships, product launches, mergers & acquisitions, in the AI in cybersecurity market
- To analyze the impact of macroeconomic factors on AI in cybersecurity market across all regions
Available customizations:
Using the provided market data, MarketsandMarkets offers customizations tailored to the company’s specific needs. The following customization options are available for the report.
Product Analysis
- Product comparative analysis, which gives a detailed comparison of innovative products being offered by prominent vendors
Geographic Analysis
- Further breakup of additional European countries by offering, security type, application, and vertical.
- Further breakup of additional Asia Pacific countries by offering, security type, application, and vertical.
- Further breakup of additional Middle East & African countries by offering, security type, application, and vertical.
- Further breakup of additional Latin American countries by offering, security type, application, and vertical.
Company Information
- Detailed analysis and profiling of additional market players (up to five)
Need a Tailored Report?
Customize this report to your needs
Get 10% FREE Customization
Customize This ReportPersonalize This Research
- Triangulate with your Own Data
- Get Data as per your Format and Definition
- Gain a Deeper Dive on a Specific Application, Geography, Customer or Competitor
- Any level of Personalization
Let Us Help You
- What are the Known and Unknown Adjacencies Impacting the AI in Cybersecurity Market
- What will your New Revenue Sources be?
- Who will be your Top Customer; what will make them switch?
- Defend your Market Share or Win Competitors
- Get a Scorecard for Target Partners
Custom Market Research Services
We Will Customise The Research For You, In Case The Report Listed Above Does Not Meet With Your Requirements
Get 10% Free CustomisationTESTIMONIALS














Growth opportunities and latent adjacency in AI in Cybersecurity Market