
Middle East and Africa Cybersecurity Market
Middle East & Africa Cybersecurity Market by Solution (IAM, Firewall, Log Management & SIEM, Compliance), Service (Professional [Risk & Threat Management, Consulting, Training], Managed), Security Type (Cloud, Application, Network) - Forecast to 2030




OVERVIEW
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
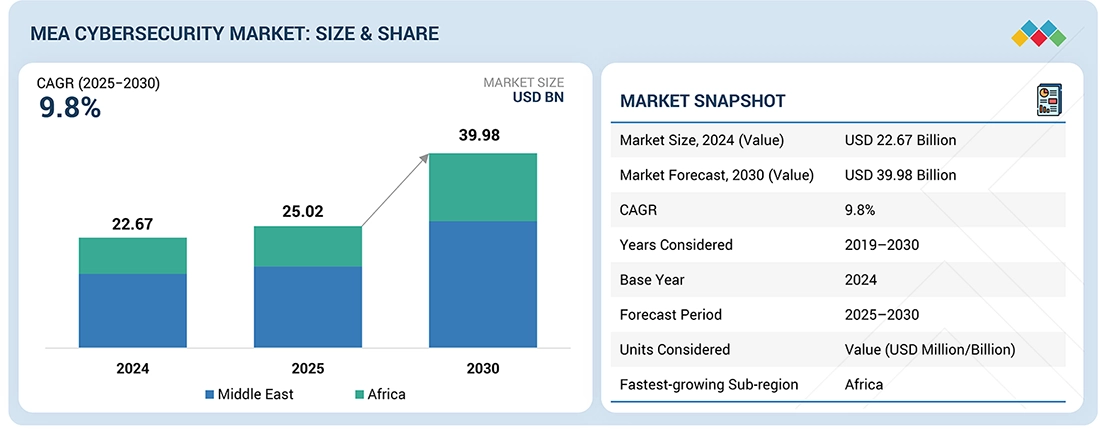
The MEA cybersecurity market size is expected to grow from USD 25.02 billion in 2025 to USD 39.98 billion by 2030, at a growth rate of 9.8% during the forecast period. This growth can be attributed mainly to the rapid expansion of digital infrastructure and the rising cyber risk exposure. In Sub-Saharan Africa, the rising fintech and mobile money services have led to increased digital transactions, which have exposed the region to rising cyber risks such as phishing, fraud, and identity-based attacks. INTERPOL's Africa Cyberthreat Assessment report lists online fraud as one of the top-rated cyber threats within the region.
KEY TAKEAWAYS
-
BY SUB-REGIONThe Middle East is estimated to account for ~67% share of the Middle East & Africa cybersecurity market in 2025.
-
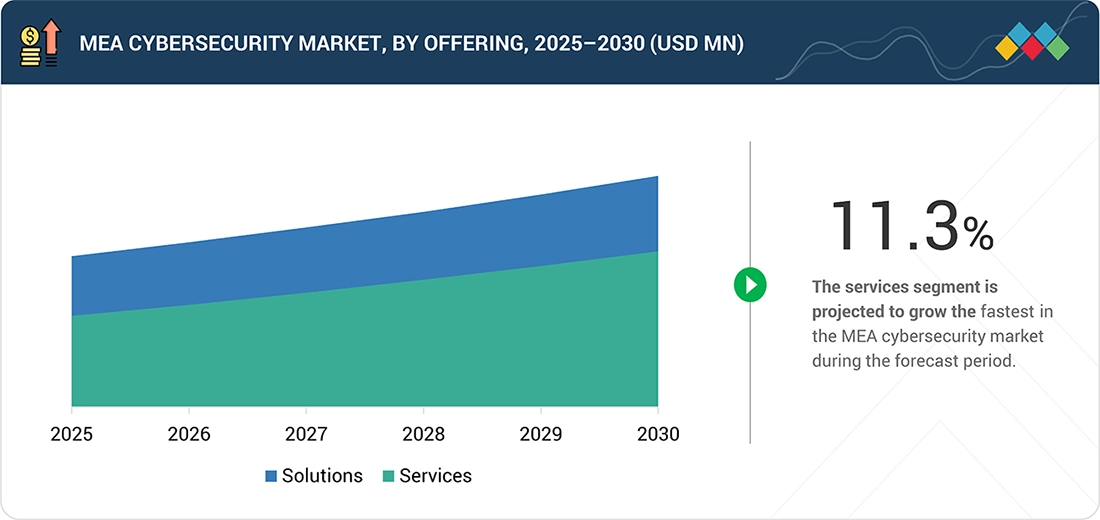
BY OFFERINGThe services segment is expected to register the highest CAGR of 11.3% during the forecast period.
-
BY SOLUTION TYPEThe log management & SIEM segment is dominating the market.
-
BY SECURITY TYPEThe cloud security segment is expected to register the highest CAGR of 12.2% during the forecast period.
-
BY DEPLOYMENT MODECloud deployment of cybersecurity is projected to grow the fastest from 2025 to 2030.
-
BY ORGANIZATION SIZESMEs are growing the fastest during the forecast period.
-
BY VERTICALThe healthcare & life sciences segment is projected to grow the fastest during the forecast period.
-
COMPETITIVE LANDSCAPE - KEY PLAYERSLeading players in the MEA cybersecurity market include Cisco, Palo Alto Networks, Fortinet, IBM, Check Point, and Trend Micro, supported by strong enterprise presence, broad security portfolios, and established regional partner ecosystems across key industries.
-
COMPETITIVE LANDSCAPE - STARTUPSEmerging MEA cybersecurity players include SpiderSilk, specializing in offensive security, threat intelligence, and digital risk protection; RAS Infotech, delivering network, cloud, and zero trust solutions through regional vendor partnerships; and CyberSec Consulting, focused on governance, risk, compliance advisory, and penetration testing services across enterprises and public sector organizations.
Digital transformation initiatives within the MEA region are contributing to the growth of the cybersecurity market. Digital platforms such as the GITEX Africa event focus on the development of secure cloud infrastructure and AI-driven security innovations as key digital transformation enablers for the regional economy. In addition, governments are focusing on the development of digital awareness and workforce development programs, such as the Nebras cyber safety initiative launched by the UAE, which aims to develop a robust cyber risk landscape for the overall economy.
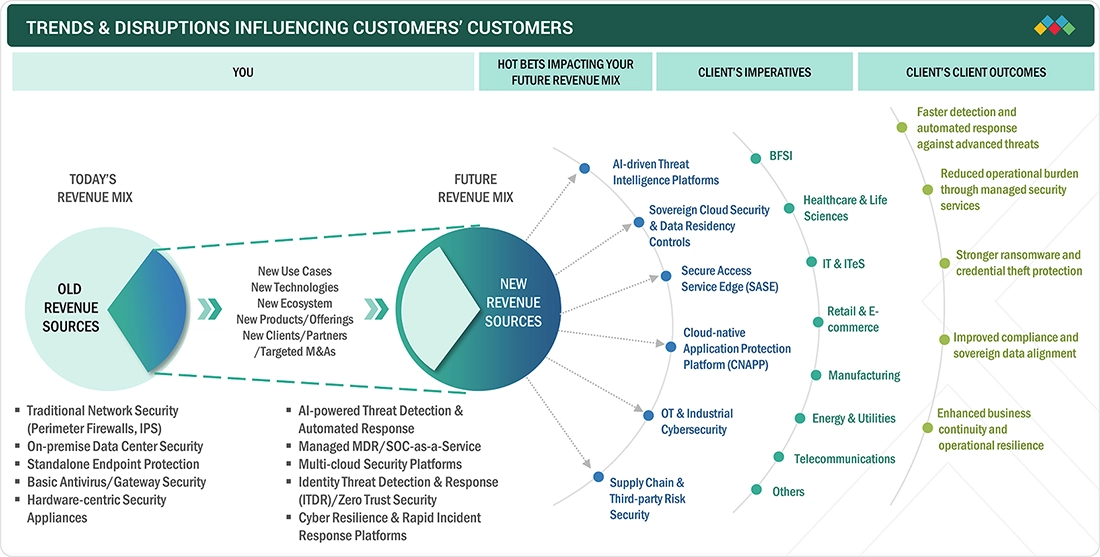
TRENDS & DISRUPTIONS IMPACTING CUSTOMERS' CUSTOMERS
The MEA cybersecurity market is shifting from traditional perimeter-based and hardware-centric security to a converged, AI-based, and service-centric security paradigm. Current revenues are largely based on network security, endpoint security, etc., whereas the future growth drivers are expected to be based on AI-based threat intelligence, sovereign cloud security, secure access service edge, identity threat detection, cyber resilience, etc. Furthermore, the adoption of cybersecurity solutions is increasing across BFSI, government, healthcare, energy, telecom, manufacturing industries, etc., as they seek faster detection, regulatory compliance, ransomware protection, operational resilience, etc., within complex hybrid and multi-cloud environments.
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
MARKET DYNAMICS
Level
-
Government-led Digital Transformation & Sovereign Cloud Mandates

-
Escalating Cyber Threat Sophistication
Level
-
Cybersecurity Skill Shortage
-
Budget Constraints in Non-GCC and African Markets
Level
-
Rise of AI-integrated Security Platforms
-
Growth of Cybersecurity Localization and Regional Ecosystems
Level
-
Integration Complexity Across Hybrid and Legacy Environments
-
Regulatory Fragmentation Across MEA Countries
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
Driver: Government-led Digital Transformation & Sovereign Infrastructure
Digitalization initiatives undertaken by governments are creating a strong growth accelerator for cybersecurity demand in MEA countries. The governments of MEA countries, namely the UAE and Saudi Arabia, are embracing cybersecurity as a component of their cloud computing strategy, AI strategy, and smart government strategy. For example, the UAE has enhanced its national cybersecurity ecosystem through public-private partnerships and AI-driven initiatives for enhancing cybersecurity resilience. Additionally, Saudi Arabia launched new cybersecurity investment programs during Black Hat MEA to improve cybersecurity capabilities within the country.
Restraint: Cybersecurity Skill Shortage
The lack of skilled cybersecurity personnel or experts is one of the major constraints within the MEA cybersecurity landscape, particularly outside the Gulf countries. The pace of digitalization and threat sophistication is far outpacing the availability of skilled security analysts, SOC specialists, and threat intelligence experts. The lack of skilled personnel acts as a constraint on the development of internal skills and the adoption of sophisticated security architectures, particularly within the emerging Middle East and African markets.
Opportunity: Expansion of Managed Detection and Response (MDR) Services
Skill shortage and hybrid IT environments are providing significant growth opportunities for managed security services in the MEA. The organizations are increasingly adopting outsourced SOC operations and AI-based monitoring services to ease operational burden and quicken response times. Regional collaborations, such as the cybersecurity partnerships announced at GISEC Global, are also indicating the growing need for integrated MDR and threat management services.
Challenge: Regulatory Fragmentation Across MEA
Regulatory requirements for cybersecurity differ substantially between the countries of the GCC, the Rest of Middle East, and African countries. Data protection laws, sector-specific regulatory requirements, and data residency requirements add complexity for MNEs operating in the region. Organizations face the challenge of adapting to the ever-changing national cybersecurity landscape, including data sovereignty regulations and sector-specific regulatory requirements, which add complexity and operational costs.
MIDDLE EAST AND AFRICA CYBERSECURITY MARKET: COMMERCIAL USE CASES ACROSS INDUSTRIES
| COMPANY | USE CASE DESCRIPTION | BENEFITS |
|---|---|---|
 |
After a major Shamoon malware attack disrupted its IT systems, Saudi Aramco implemented Symantec’s Advanced Threat Protection solution to strengthen threat detection, improve real-time response, and enhance visibility across its critical infrastructure. | Strengthened cybersecurity posture | Real-time detection and response to advanced threats | Improved visibility and centralized IT control | Faster containment of malware incidents | Reduced operational disruption and improved resilience |
 |
In response to a targeted ATM malware incident that compromised its banking systems, SABB implemented Palo Alto Networks’ Next Generation Firewall solution to reinforce network defenses, strengthen advanced threat detection, and improve centralized visibility across its IT and ATM infrastructure. | Improved protection against advanced and ATM-targeted malware | Enhanced real-time threat detection and prevention capabilities | Greater visibility across network traffic and systems | Reduced risk of financial losses from cyberattacks | Faster response to potential security breaches |
 |
Following a sophisticated phishing campaign that compromised customer credentials and targeted its online banking platform, NBK deployed Fortinet’s Unified Threat Management solution to strengthen threat detection, enhance network visibility, and secure digital banking operations against advanced attacks. | Enhanced protection against phishing and credential-based attacks | Improved threat detection and prevention across online banking systems | Greater visibility and control over network traffic | Reduced risk of financial fraud and customer data compromise | Strengthened overall cybersecurity risk management capabilities |
Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET ECOSYSTEM
The MEA cybersecurity vendor landscape comprises some of the world’s leading technology players, along with some specialist vendors. The global vendors include Palo Alto Networks, Fortinet, Cisco Systems, Microsoft, IBM, Check Point, and AWS, which are the dominant players in the network security, cloud security, identity security, and advanced threat management markets. On the other hand, the regional vendors and system integrators offer country-specific cybersecurity solutions. Overall, the cybersecurity vendor landscape in the MEA is well balanced, with the global platform vendors providing the basic cybersecurity infrastructure, while the regional vendors increase the depth of the cybersecurity market through their specialized offerings.
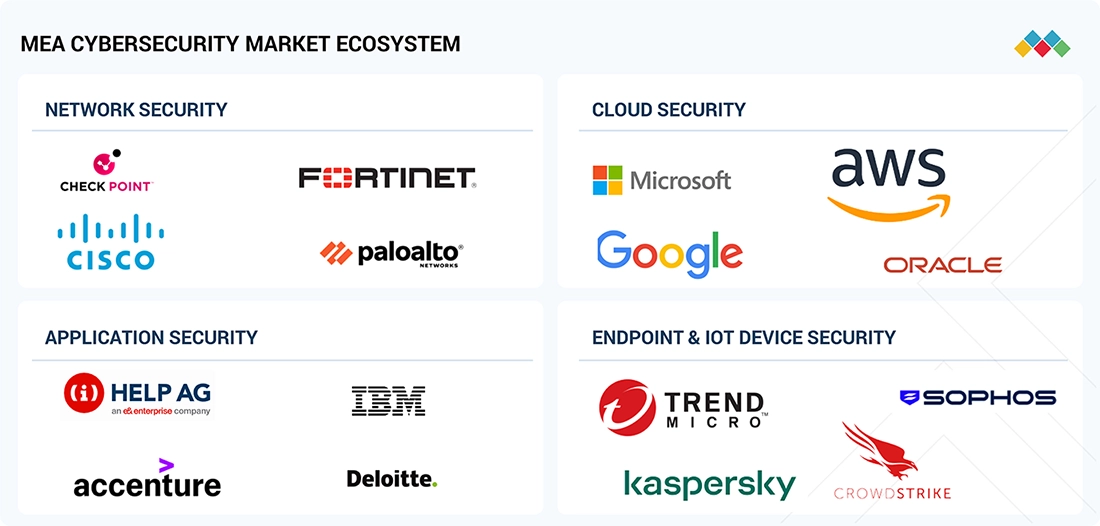
Logos and trademarks shown above are the property of their respective owners. Their use here is for informational and illustrative purposes only.
MARKET SEGMENTS
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
MEA Cybersecurity Market, By Offering
The solutions segment held the largest market share in the MEA cybersecurity market, due to consistent investment patterns in traditional security infrastructure, including the government, BFSI, telecom, and energy sectors. Organizations continue to invest in network firewalls, cloud security platforms, identity protection, and sophisticated threat detection tools for the growing digital landscape. Cybersecurity initiatives in countries like Saudi Arabia and the UAE are driving the purchase of integrated solutions, as opposed to individual services. Though managed services are growing steadily, solutions are ahead in terms of adoption, driven by the need to enhance core security infrastructure and comply with regulations.
MEA Cybersecurity Market, By Solution Type
Log management and Security Information and Event Management (SIEM) solutions are the largest segment in the MEA market, driven by the rising demand for central visibility and regulatory reporting. Organizations across the government, telecom, and BFSI sectors are increasingly deploying SIEM solutions to centralize log data, detect anomalies, and offer real-time response to security incidents. National cybersecurity strategies mandate continuous monitoring and audit, thereby boosting the adoption of SIEM solutions. With the move of enterprises to integrated SOC platforms, log analytics and threat correlation continue to be integral to the cybersecurity ecosystem of the region.
MEA Cybersecurity Market, By Security Type
Network security was the largest segment of the MEA cybersecurity market; this is driven by the rapid deployment of 5G networks, data center infrastructure, and the rise of connected devices in hybrid IT and OT ecosystems. Industries such as oil and gas, telecom, and banking heavily invest in sophisticated firewalls, intrusion prevention systems, and secure access solutions. The sharp increase in DDoS attacks has also spurred investment in network traffic monitoring systems. With the development of new connectivity infrastructure, network layer security remains a prime focus for cybersecurity.
MEA Cybersecurity Market, By Deployment Mode
On-premises deployment maintains the largest share of the market in the MEA region, especially in government, defense, BFSI, and other sectors, wherein data sovereignty and data compliance are of paramount importance to them. Most of the organizations prefer to maintain data and security operations in their own premises in their respective countries. Cloud deployment is also increasing, as sovereign cloud initiatives in Gulf economies are encouraging the adoption of a hybrid approach wherein critical workloads are being hosted in on-premises environments. The need for data residency and infrastructure protection continues to drive the demand for on-premises cybersecurity solutions across the region.
MEA Cybersecurity Market, By Organization Size
Large businesses account for a major share of the MEA cybersecurity market due to the complexity of the IT infrastructure, the international nature of the businesses, and the high degree of exposure to sophisticated cyber threats. Large banks, telecom providers, oil and gas corporations, and governments require large budgets for integrated cybersecurity platforms, artificial intelligence-based monitoring systems, and sophisticated threat intelligence platforms. For example, national oil companies and financial institutions have invested heavily in detection and response systems following high-profile cyber attacks. In terms of the sheer size of the businesses, large enterprises are the main contributors to the revenue generated for the regional cybersecurity market.
MEA Cybersecurity Market, By Vertical
The BFSI sector dominates the MEA cybersecurity market share, given the growth rate of digital banking services, the expansion of the fintech industry, and the increasing transactional volume of the economies of the Gulf countries and Africa. Financial services companies face constant threats like phishing, ransomware, and credential stealing, which makes the adoption of fraud detection, identity management, and real-time monitoring solutions a necessity. As the digital payment infrastructure develops, financial institutions and fintech players lead the adoption of cybersecurity solutions.
REGION
By sub-region, the Middle East is dominating the MEA cybersecurity market
The Middle East holds the largest share of the MEA cybersecurity market, backed by robust digital transformation strategies driven by governments, mature enterprise landscapes, and robust regulatory environments. Countries such as the UAE and Saudi Arabia continue to invest heavily in national cybersecurity, cloud, and critical infrastructure protection. On the other hand, the African market is expected to grow the fastest in the coming years. The digitalization of the region, development of fintech and mobile money services, and high internet penetration, as well as an increase in cyberattack cases, are boosting the adoption of cloud, identity, and managed security across emerging economies in Africa.

MIDDLE EAST AND AFRICA CYBERSECURITY MARKET: COMPANY EVALUATION MATRIX
The MEA cybersecurity market has a competitive mix of both global platform leaders and new innovators. Global technology leaders, such as Cisco, maintain a dominant position with comprehensive network security, cloud security, and integrated threat intelligence. On the other hand, emerging companies such as Trellix are growing rapidly with advanced detection, threat intelligence, and AI-powered security operations capabilities. Throughout the region, vendors are strengthening sovereign cloud alignment, identity security frameworks, and cyber resilience solutions to meet regulatory requirements and support digital transformation initiatives across government and enterprise sectors.
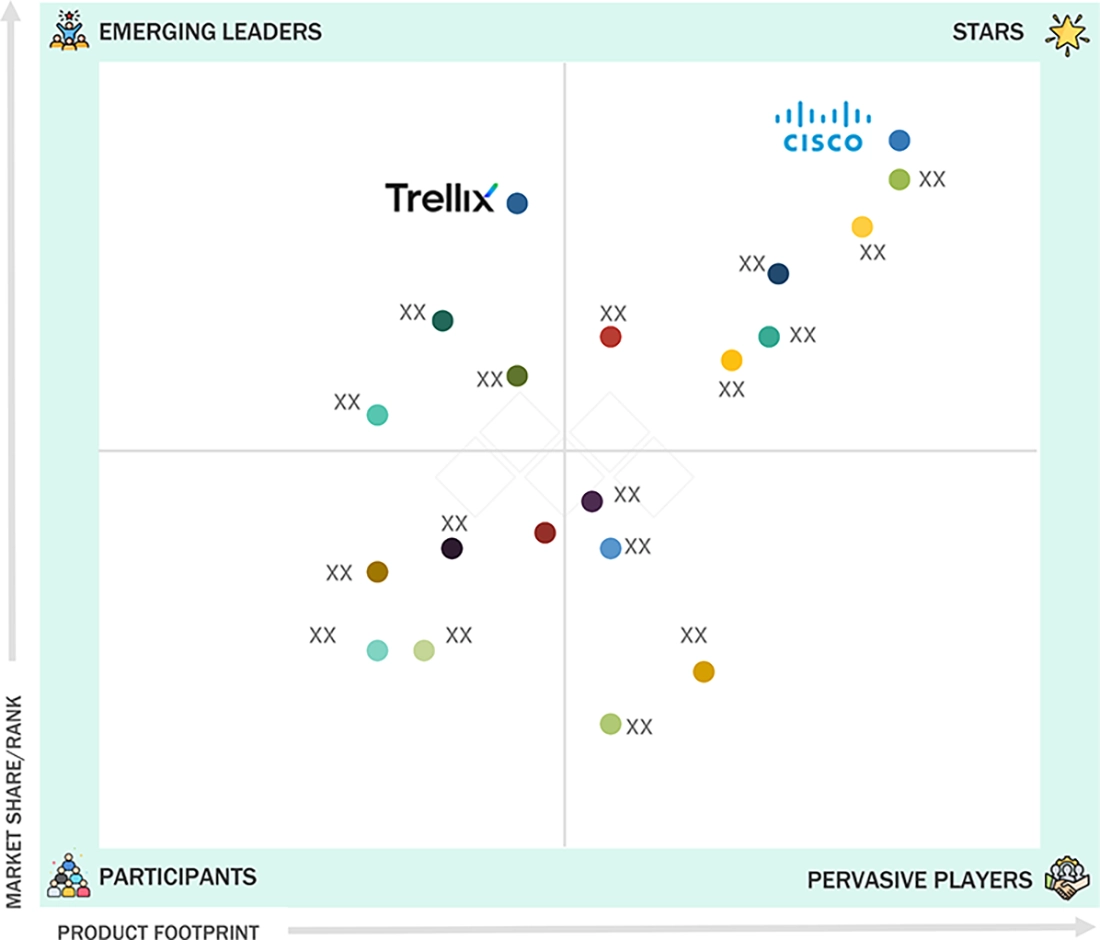
Source: Secondary Research, Interviews with Experts, MarketsandMarkets Analysis
KEY MARKET PLAYERS
- IBM (US)
- Cisco (US)
- Palo Alto Networks (US)
- Check Point (US/Israel)
- Trend Micro (Japan)
- Fortinet (US)
- Norton Lifelock (US)
- Sophos (UK)
- Kaspersky (Russia)
- Trellix (US)
- ESET (Slovakia)
- Edge Group (UAE)
- BEACON RED (UAE)
- Moro Hub (UAE)
MARKET SCOPE
| REPORT METRIC | DETAILS |
|---|---|
| Market Size, 2024 (Value) | USD 22.67 Billion |
| Market Forecast, 2030 (Value) | USD 39.98 Billion |
| Growth Rate | CAGR of 9.8% from 2025 to 2030 |
| Years Considered | 2019–2030 |
| Base Year | 2024 |
| Forecast Period | 2025–2030 |
| Units Considered | Value (USD Million/Billion) |
| Report Coverage | Revenue Forecast, Company Ranking, Competitive Landscape, Growth Factors, and Trends |
| Segments Covered |
|
| Regions Covered | Middle East and Africa |
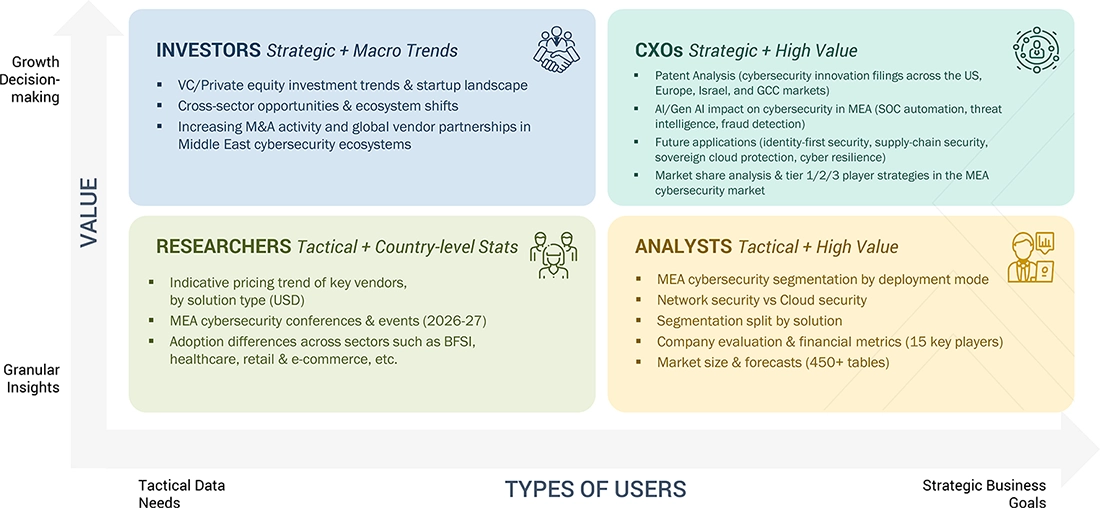
WHAT IS IN IT FOR YOU: MIDDLE EAST AND AFRICA CYBERSECURITY MARKET REPORT CONTENT GUIDE
DELIVERED CUSTOMIZATIONS
We have successfully delivered the following deep-dive customizations:
| CLIENT REQUEST | CUSTOMIZATION DELIVERED | VALUE ADDS |
|---|---|---|
| Market Comparison & Dynamics Evaluation | Delivered detailed analysis of MEA cybersecurity market dynamics, including segmentation by offering, solution type, security type, deployment mode, organization size, and vertical. Assessed key growth drivers, restraints, opportunities, and evolving enterprise demand patterns across industries. | Provided clear visibility into market structure, high-growth segments, and shifting demand trends, enabling stronger alignment of business strategy with MEA's evolving cybersecurity landscape. |
| Competitive Intelligence Assessment | Conducted competitive landscape analysis covering global technology vendors, regional MEA cybersecurity providers, and emerging specialists. Included ecosystem mapping, vendor positioning (star players vs. emerging leaders), and strategic developments such as partnerships, expansion initiatives, and service-led growth strategies. | Enhanced understanding of competitive positioning and differentiation within MEA, supporting strategic benchmarking, partnership evaluation, and go-to-market planning. |
| Product Analysis & Capability Benchmarking | Performed product and capability analysis comparing vendors across key cybersecurity domains, including AI-driven threat detection, SIEM, cloud security, identity & access management, managed security services, and deployment models (cloud, hybrid, and on-premises). | Enabled clearer portfolio benchmarking, identification of capability gaps, and alignment of offerings with enterprise digital transformation, cloud adoption, and evolving cybersecurity demand across the Middle East & Africa. |
RECENT DEVELOPMENTS
- November 2025 : KPMG signed a partnership agreement with Fortinet to enhance cybersecurity services across the region. The partnership aimed to deliver integrated cyber risk management, network security, zero trust frameworks, and secure digital transformation solutions for enterprises and government entities.
- September 2025 : IBM and AWS expanded their strategic collaboration in the Middle East to accelerate secure cloud adoption. The collaboration focused on enabling enterprise digital transformation, enhancing cybersecurity integration within hybrid cloud environments, and supporting regulatory-compliant and resilient cloud infrastructure deployments.
- April 2025 : Check Point Software Technologies announced its participation at GISEC Global 2025 in Dubai as a Diamond Sponsor, collaborating with AWS, WIZ, Radware, and TechBridge Distribution MEA. The partnership focuses on advancing AI-powered threat prevention, multi-cloud security, and automated cyber defense solutions, strengthening cyber resilience across the UAE’s public and private sector organizations while expanding regional investments and local ecosystem collaboration.
Table of Contents

Methodology
This study involved multiple steps in estimating the current size of the Middle East and Africa Cybersecuty market. Exhaustive secondary research was carried out to collect information on the Middle East and Africa Cybersecurity industry. The next step was to validate these findings, assumptions, and sizing with industry experts across the value chain using primary research. The top-down and bottom-up approaches were employed to estimate the total market size. After that, the market breakup and data triangulation procedures were used to estimate the market size of the segments and subsegments.
Secondary Research
Secondary sources referred to for this research study include financial statements of companies offering cybersecurity solutions/ services and information from various trade, business, and professional associations. The secondary data was collated and analysed to arrive at the overall size of the Middle East and Africa Cybersecurity market, which was validated by primary respondents.
Primary Research
Extensive primary research was conducted after obtaining information regarding the Middle East and Africa Cybersecurity market scenario through secondary research. Several primary interviews were conducted with market experts from both, the demand and supply sides across major countries of Middle East and Africa. Primary data was collected through questionnaires, emails, and telephonic interview. The primary sources from the supply side included various industry experts, such as Chief X Officers (CXOs), Vice Presidents (VPs), Directors, from business development, marketing, product development/innovation teams, and related key executives from Middle East and Africa Cybersecurity vendors; system integrators; component providers; distributors; and key opinion leaders.
Primary interviews were conducted to gather insights such as market statistics, data of revenue collected from the products and services, market breakdowns, market size estimations, market forecasting, and data triangulation. Primary research also helped in understanding the various trends related to technology, application, vertical, and region. Stakeholders from the demand side, such as CIOs, CTOs, and CSOs, and installation teams of the customer/end users who are using cybersecurity solutions/services were interviewed to understand the buyer's perspective on the suppliers, products, component providers, and their current usage of cybersecurity solutions/services and future outlook of their business which will affect the overall market.
To know about the assumptions considered for the study, download the pdf brochure
Market Size Estimation
In the market engineering process, top-down and bottom-up approaches were extensively used, along with several data triangulation methods, to perform the market estimation and market forecasting for the overall market segments and sub-segments listed in this report. Extensive qualitative and quantitative analysis was performed on the complete market engineering process to list key information/insights throughout the report. This entire procedure included the study of the annual and financial reports of top market players and extensive interviews for key insights from industry leaders, such as CEOs, VPs, directors, and marketing executives. All percentage splits and breakups were determined using secondary sources and verified through primary sources. All possible parameters that affect the market covered in this research study have been accounted for, viewed in extensive detail, verified through primary research, and analyzed to get the final quantitative and qualitative data. This data is consolidated and added to detailed inputs and analysis from MarketsandMarkets.
Data Triangulation
After arriving at the overall market size using the market size estimation processes explained above, the market was split into several segments and subsegments. The data triangulation and market breakup procedures were employed, wherever applicable, to complete the overall market engineering process and arrive at the exact statistics of each market segment and subsegment. The data was triangulated by studying various factors and trends from both the demand and supply sides.
Market Definition
Cybersecurity refers to a collection of technologies, procedures, and methods used to strengthen critical systems, including networks, physical devices, software, and information, against unauthorized access, insider threats, and malicious attacks. Such attacks can disrupt data transmission across networks, lead to operational disruptions, and result in extortion or ransom demands. Cybersecurity, which is also known as information security, can be provided through hardware, software, and services.
Key Stakeholders
- Government Bodies and Public Safety Agencies
- Project Managers
- Developers
- Business Analysts
- Quality Assurance (QA)/Test Engineers
- Cybersecurity Specialists
- Cybersecurity Solution and Service Providers
- Consulting Firms
- Third-party Vendors
- Investors and Venture Capitalists
- System Integrators (SIs)
- Technology Providers
Report Objectives
- To define, describe, and forecast the Middle East and Africa cybersecurity market based on components, software, services, security types, deployment modes, organization sizes, verticals, and regions
- To provide detailed information about the major factors (drivers, opportunities, restraints, and challenges) influencing the growth of the market
- To forecast the market size across two main regions: the Middle East and Africa
- To analyze subsegments of the market with respect to individual growth trends, prospects, and contributions to the overall market
- To profile the key players of the market and comprehensively analyze their market size and core competencies
- To profile key players and comprehensively analyze their market rankings and core competencies
- To map the companies to get competitive intelligence based on company profiles, key player strategies, and game-changing developments, such as product developments, collaborations, and acquisitions
- To track and analyze the competitive developments, such as product enhancements and new product launches; acquisitions; and partnerships and collaborations, in the Middle East and Africa cybersecurity market
Available Customization
MarketsandMarkets offers the following customization for this market report:
- Additional country-level analysis of the Middle East and Africa Cybersecurity Market
- Profiling of additional market players (up to 5)
Product Analysis:
- Product matrix, which provides a detailed comparison of the product portfolio of each company in the Middle East and Africa Cybersecurity Market.
Need a Tailored Report?
Customize this report to your needs
Get 10% FREE Customization
Customize This ReportPersonalize This Research
- Triangulate with your Own Data
- Get Data as per your Format and Definition
- Gain a Deeper Dive on a Specific Application, Geography, Customer or Competitor
- Any level of Personalization
Let Us Help You
- What are the Known and Unknown Adjacencies Impacting the Middle East & Africa Cybersecurity Market
- What will your New Revenue Sources be?
- Who will be your Top Customer; what will make them switch?
- Defend your Market Share or Win Competitors
- Get a Scorecard for Target Partners
Custom Market Research Services
We Will Customise The Research For You, In Case The Report Listed Above Does Not Meet With Your Requirements
Get 10% Free Customisation













Growth opportunities and latent adjacency in Middle East & Africa Cybersecurity Market